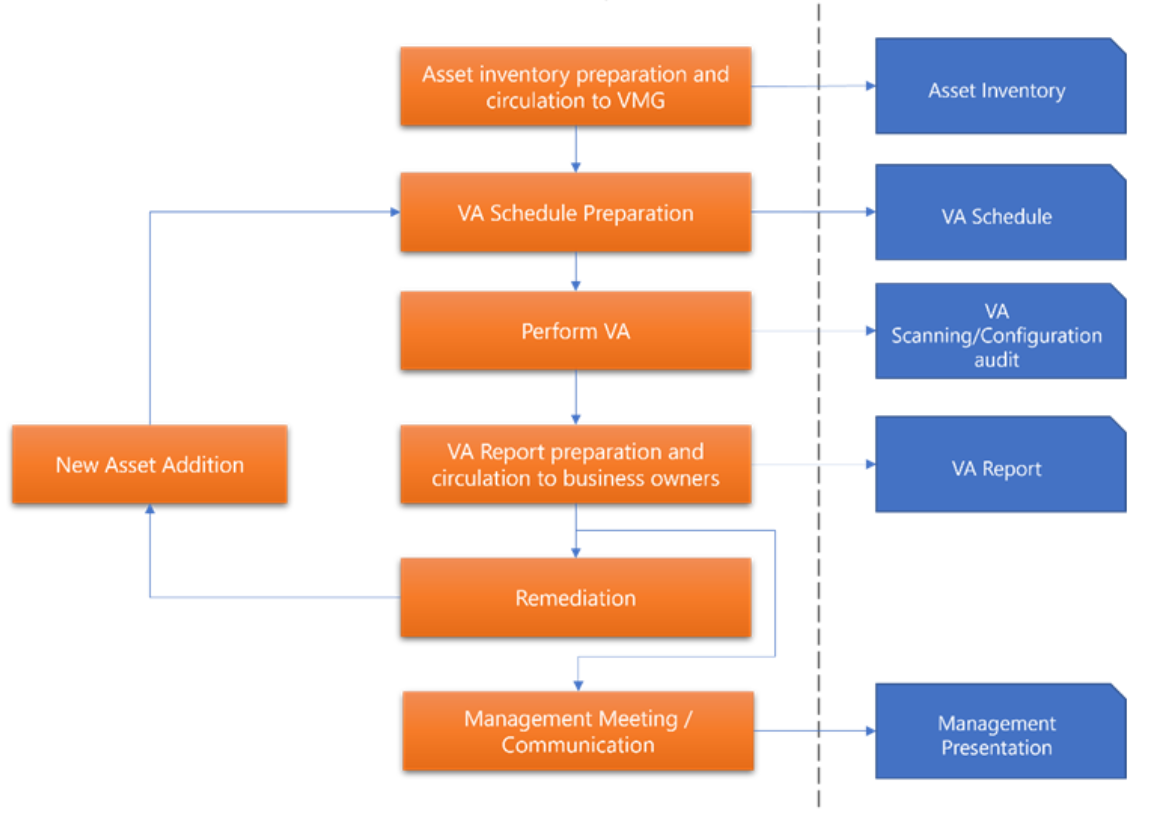
Vulnerability assessment is “The systematic examination of a system to identify those critical infrastructure or related components that may be at risk from an attack and the determination of appropriate procedures that can be implemented to reduce that risk.” Vulnerability assessment tools evaluate network-attached devices (servers, desktops, switches, routers, etc) for vulnerabilities or potentially vulnerable situations. Most vulnerabilities discovered by these tools result from software flaws, but some tools provide analysts the data necessary to discover design, implementation and configuration vulnerabilities. The VA consists of multiple phases as given in the figure below: